Complete Guide to Transparent Proxies: Pros, Cons, and Use Cases
In today's increasingly complex network technology, the term "proxy" is no longer new.
However, among the various proxy modes, the "transparent proxy" has become a core technology in scenarios such as enterprise networking, public Wi-Fi management, and home gateway acceleration due to its feature of requiring no client configuration.
This article will deeply analyze the working principles, core advantages and disadvantages of transparent proxies, as well as typical application scenarios in real life.
What is a Transparent Proxy?
Transparent Proxy (Transparent Proxy), also known as "intercepting proxy" or "forced proxy".
Its core definition lies in the word "transparent": clients (such as phones and computers) do not need to make any proxy protocol settings, and may not even be aware of the existence of the proxy server. The traffic they generate is automatically redirected to the proxy server for processing.
Brief Overview of the Working Mechanism
Transparent proxies are typically deployed at the network exit (such as routers or gateways).
1. Interception: When a client initiates an external request, the data packet first reaches the gateway device.
2. Redirection: The gateway intercepts the traffic based on preset rules (such as Linux's iptables or nftables) and redirects it to a local or designated proxy service.
3. Processing: The proxy service takes over the connection and initiates access to the target server on behalf of the client based on the request content.
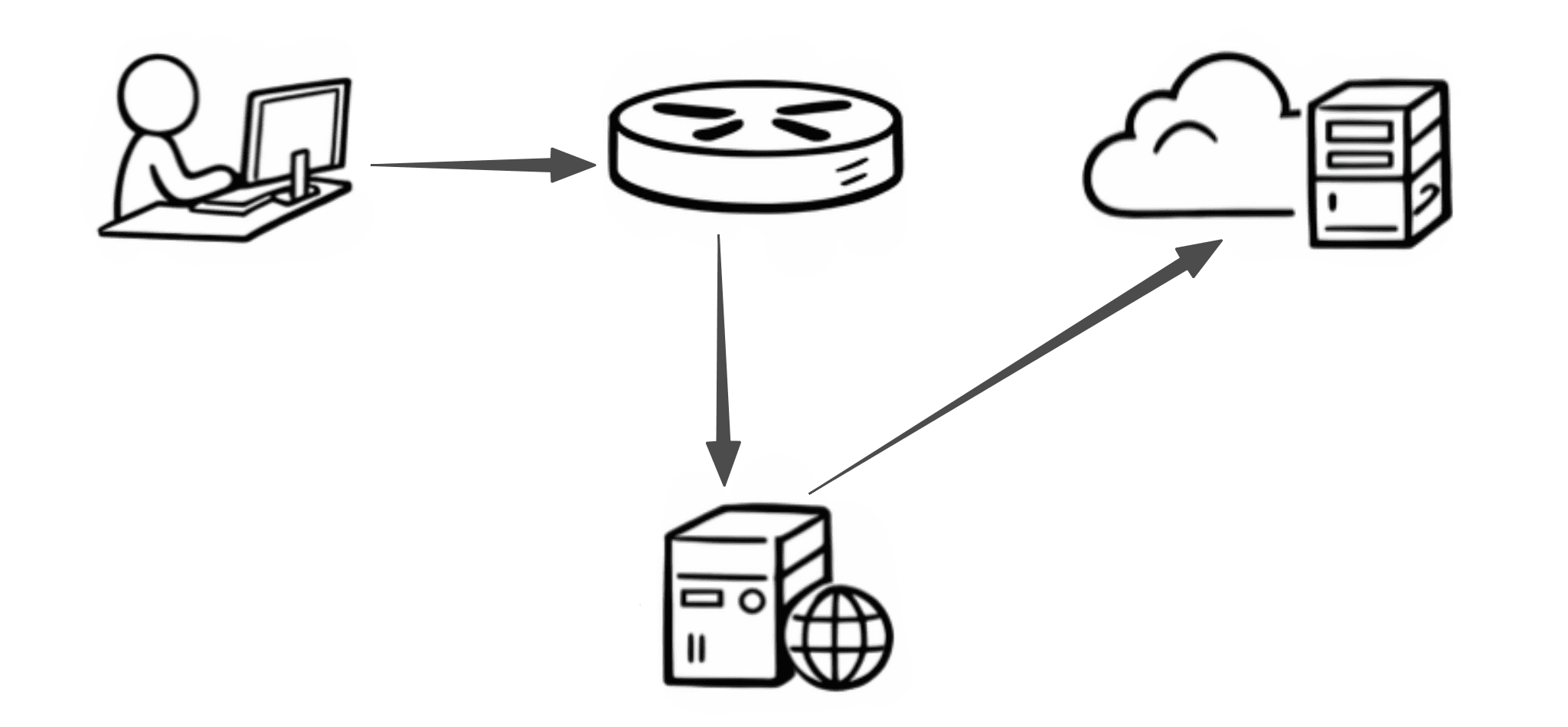
4. Return: The response from the target server is returned to the client via the proxy.
For the client, the entire communication process remains "transparent", appearing as if it is directly connected to the target server.
Advantages of Transparent Proxies
1. Zero Configuration Access
This is the biggest selling point of transparent proxies. For administrators, there is no need to manually set up proxies on hundreds or thousands of terminal devices, greatly reducing operational costs.
For users, as long as they connect to the network, all acceleration, filtering, or auditing functions take effect immediately.
2. Cross-Device and Cross-Application Support
Many smart home devices (such as smart TVs and smart speakers) or legacy software do not support manual proxy settings. Transparent proxies can intercept traffic at the network layer (L3/L4), allowing them to forcefully cover all traffic, truly achieving a "family bucket" style network takeover.
3. Centralized Management and Auditing
In enterprise environments, transparent proxies can serve as a central node to uniformly implement security policies. For example, prohibiting access to malicious domains, real-time scanning for viruses in traffic, recording access logs, etc., while employees cannot bypass supervision by canceling browser proxy settings.
4. Improved Network Efficiency (Caching Mechanism)
By introducing caching functions (such as Squid) in transparent proxies, commonly used static resources (images, update packages) can be stored locally. When multiple users access the same content, the proxy directly returns the cache, saving bandwidth and reducing latency.
Potential Disadvantages and Challenges
Although transparent proxies seem perfect, they also face many tricky issues in actual deployment:
1. Conflict with Certificates and Encryption (HTTPS)
This is the biggest challenge currently facing transparent proxies. Since HTTPS is designed to prevent man-in-the-middle attacks (MITM), the behavior of intercepting traffic by transparent proxies is essentially a form of man-in-the-middle operation.
If it is just simple traffic forwarding, the proxy cannot read encrypted content.
If content filtering is required (such as blocking specific URLs), the proxy must install a self-signed root certificate (CA), which is cumbersome to operate on mobile devices and poses security risks.
2. Performance Bottlenecks
Since all network traffic must go through the interception and unpacking process at the gateway, this places high demands on the gateway hardware (CPU and memory). If the proxy service goes down, the risk of network disconnection for the entire local area network will also increase.
3. IP Spoofing and Traceability Issues
Although transparent proxies operate at the transport layer, if configured improperly, the target server will see the IP of the proxy server rather than the real client IP. This may lead to misjudgments in certain IP-based authentication or risk control systems.
Typical Use Cases
1. Enterprise Network Security Management
Many companies use transparent proxies to implement DLP (Data Loss Prevention). By intercepting employees' outbound traffic, the system can automatically identify and block document uploads containing sensitive keywords or company secrets.
2. Home/Small Office Gateway Acceleration
In enthusiast circles, transparent proxies are often deployed using "bypass routers" or "main routers." By configuring diversion rules at the gateway, the following can be achieved:
· Automatic acceleration for overseas access (such as speeding up GitHub).
· Full network ad blocking: removing ad domain names before traffic enters the device.
3. Captive Portal for Public Wi-Fi Authentication
The login page that automatically redirects you after connecting to Wi-Fi at airports or hotels is powered by transparent proxies. It intercepts your initial HTTP request and forces you to redirect to the authentication gateway.
4. Content Filtering in Educational and Research Institutions
School libraries often use transparent proxies to restrict access to specific categories of websites or provide a unified exit for off-campus access to academic resources (such as IEEE, CNKI).
Transparent Proxy vs. Explicit Proxy
Transparent Proxy: Users do not need any configuration; traffic is automatically intercepted and forwarded to the proxy server by the network.
Explicit Proxy: This refers to the proxy IP that general users purchase, which needs to be actively configured in the system or software proxy address (IP + port).
| Dimension | Transparent Proxy | Explicit Proxy |
|---|---|---|
| Need for Configuration | ❌ No | ✅ Yes |
| User Awareness | ❌ Unaware | ✅ Aware |
| Control | Network Administrator | User |
| Support for Anonymity | ❌ Generally Not Supported | ✅ Supported |
| Deployment Location | Network Layer (Gateway/Firewall) | Client (Browser/System) |
| Typical Uses | Control, Filtering, Caching | Access, Development, Privacy |
Conclusion
Through this article, you have gained a general understanding of the basic concepts, principles, and applications of transparent proxies. For technical managers, choosing a transparent proxy means choosing "stronger control";
for ordinary users, understanding the working principles of transparent proxies helps to better balance the online experience with personal privacy in an increasingly complex network environment.
If you wish to further explore proxy-related knowledge, such as the differences between different types of proxies, actual deployment methods, or how to choose and optimize in specific scenarios, you can find more systematic analyses and practical guides on our website.